Final Data Audit Report – сапиасексуал, 18008742717, 18006657700, 3510387779, сыпщьфклуе
The Final Data Audit Report examines the exposure risks tied to сапиасексуал, 18008742717, 18006657700, 3510387779, and сыпщьфклуе. It documents consistent identifiers and contact details found in inventories, with gaps in data minimization and consent governance. Controls are outlined alongside gaps in de-identification and access management. The analysis points to explicit authorizations and sustained governance as essential. The document prompts further consideration of prioritized actions and milestones to close the risks, leaving a clear path forward yet unresolved at this stage.
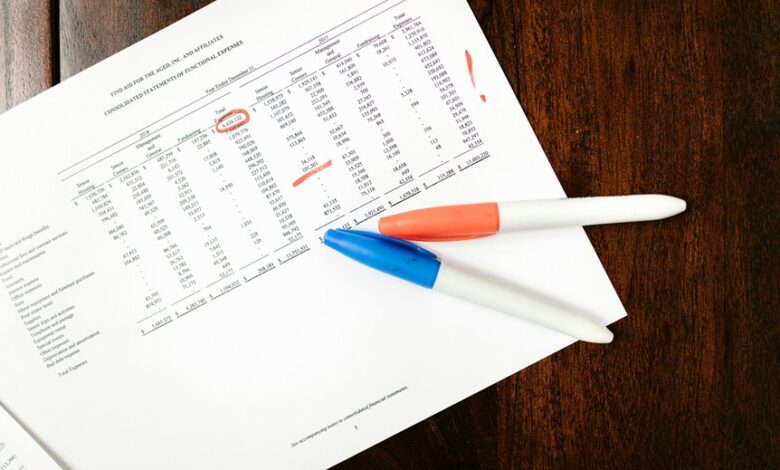
What a Final Data Audit Reveals About Sensitive Identifiers
A Final Data Audit reveals that sensitive identifiers—such as personal account numbers and contact details—are subject to consistent exposure risks across data inventories.
The assessment notes recurring gaps in data minimization and inconsistent consent management practices, emphasizing controlled access and de-identification where feasible.
Findings advocate rigorous retention limits, role-based access, and transparent consent workflows to reduce residual exposure and preserve user autonomy.
Assessing Privacy Compliance for сапиасексуал and Phone Data
The assessment builds on identified exposure risks from the Final Data Audit by examining privacy compliance for сапиасексуал and associated phone data, with particular attention to data minimization, consent management, and access controls.
Thorough evaluation centers on documented practices, regulatory alignment, and policy enforcement, ensuring privacy compliance and data minimization are maintained through minimal data collection, explicit authorizations, and robust access governance.
Risks, Controls, and Gaps You Must Address Now
Assessing the current landscape reveals that gaps in data minimization, consent governance, and access controls pose concrete risks to сапиасексуал and associated phone data.
The report identifies privacy controls, data minimization, and compliance gaps, outlining risk remediation measures and clear responsibilities.
Ongoing monitoring is essential to sustain compliance, reduce exposure, and support freedom through transparent governance and prudent data stewardship.
Practical Remediation and Ongoing Monitoring Tactics
Practical remediation and ongoing monitoring tactics focus on translating identified gaps into concrete, prioritized actions and sustained oversight.
Remediation sequences emphasize data minimization by limiting unnecessary retention and exposure, paired with measurable milestones and timelines.
Ongoing oversight leverages access governance to enforce policy changes, review role assignments, and monitor anomaly signals, ensuring continuous alignment with risk appetite and regulatory expectations.
Continuous documentation underpins reproducible accountability.
Frequently Asked Questions
What Are the Legal Implications of Data Misclassification
Legal implications of data misclassification include regulatory penalties, contractual liability, and reputational harm; organizations should integrate data governance frameworks and conduct risk assessment to mitigate exposure, enforce accountability, and ensure accurate data handling across processes.
How to Quantify Non-Compliance Penalties Precisely
Penalties are quantified via explicit statutory formulas, uplift factors, and contractual terms; in practice, data governance and risk assessment frameworks yield precise per-day, per-record, or tiered fines, calibrated to severity and breach duration. It reads like a ledger.
Which Teams Should Own the Remediation Milestones
Data ownership should assign remediation milestones to cross-functional owners; coordinated governance ensures accountability, with explicit deadlines and traceability. Each team contributes measurable progress, while risk, controls, and dependencies are documented to sustain ongoing remediation milestones.
How to Validate Third-Party Data Vendors’ Privacy Posture
Validation governance and vendor due diligence are essential to assess third-party data vendors’ privacy posture, including data handling, security controls, breach notification, and ongoing monitoring, ensuring accountability and alignment with risk appetite and regulatory expectations.
What Are the Long-Term Costs of Ongoing Monitoring Programs.
Ongoing monitoring incurs ongoing costs, potentially substantial and predictable, driven by staffing, tooling, and vendor fees. Security governance and data stewardship justify these investments as risk reduction, compliance, and operational resilience extend long-term, though budgets must remain flexible and transparent.
Conclusion
The audit reveals persistent exposure risks tied to sensitive identifiers and inconsistent consent handling, underscoring the need for reinforced access controls and data minimization. While improvements are evident in governance, gaps remain in de-identification and explicit authorizations. Actions should be prioritized, with clear milestones and ongoing monitoring. The process functions like a lighthouse, steady and precise, guiding governance toward transparent documentation and robust privacy compliance—ensuring user autonomy remains central and auditable over time.




